Automate, Govern, Secure: Protect Your Data with Dasera
Do you know where ALL your sensitive structured and unstructured data is?
NO I want improved visibility into my data stores & risk YES I want to automate data security & governance controlsAutomatically Find, Flag, and Fix Data Security Risks
Dasera is a data security posture management (DSPM) platform that automates data security and governance controls for structured & unstructured data in your cloud, on-prem and hybrid environments to protect your data throughout its entire journey.
Automatically Find, Flag, and Fix Data Security Risks
-
Contextualized Visibility
Contextualized Visibility
Complete data infrastructure visibility throughout the lifecycle, on-prem and multi-cloud, for enhanced data insights and user understanding.
-
Data Security Posture Management (DSPM)
Data Security Posture Management (DSPM)
Simplify data discovery and classification, automating policy enforcement for structured and unstructured data across on-prem, hybrid, multiple clouds.
-
Data Access Governance (DAG)
Data Access Governance (DAG)
Gain granular access insights and controls allowing enforcement of fine-grained policies and access related compliance.
-
Data Usage Risk Management
Data Usage Risk Management
Swift detection and prevention of unauthorized access and risk management while maintaining user accessibility.
-
Compliance Monitoring
Compliance Monitoring
Continuously prevent and detect data compliance violations throughout the data infrastructure.
-
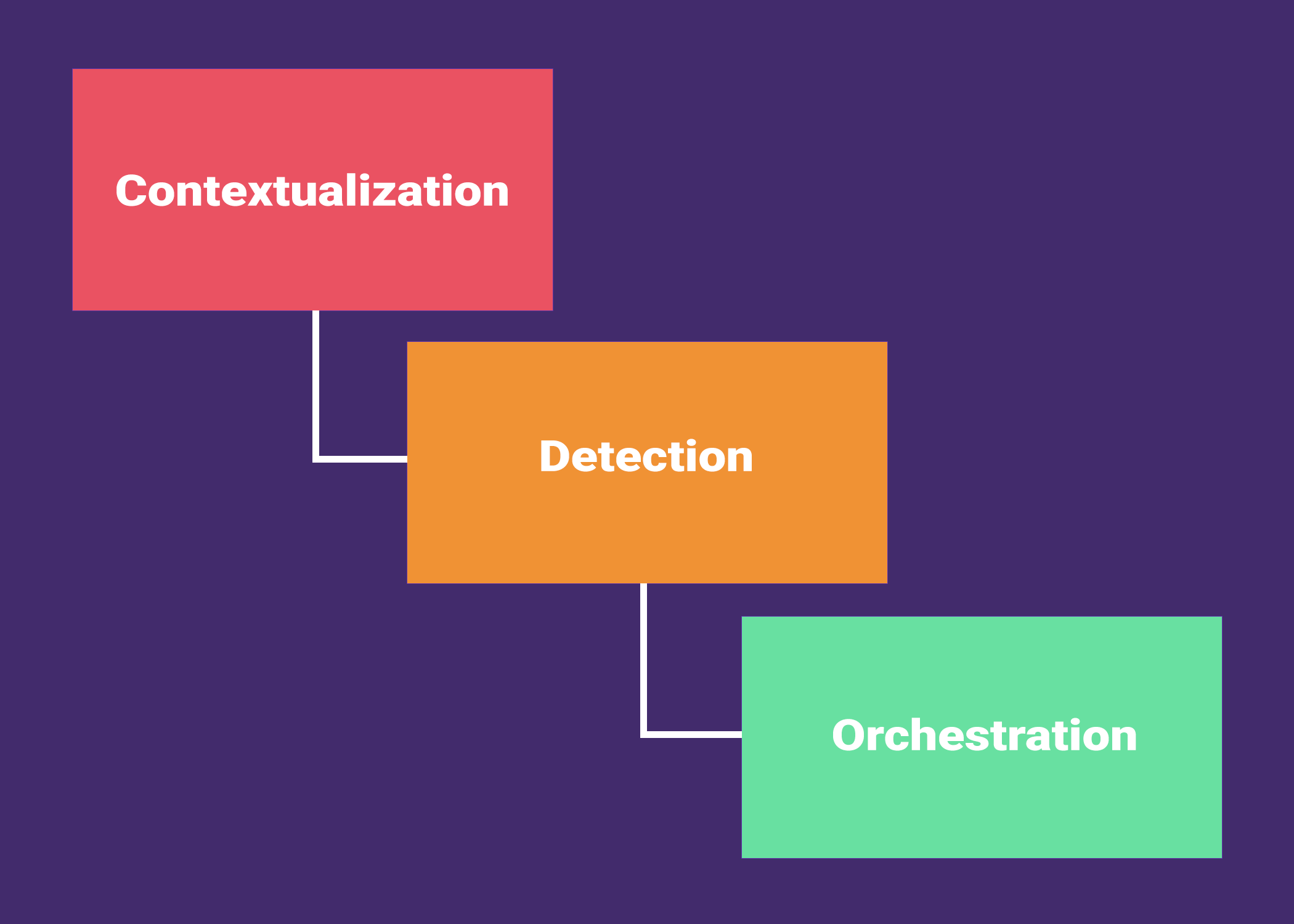
Data Detection & Response (DDR)
Data Detection & Response (DDR)
Near real time data detection with automated response capabilities including alerts, orchestration, and enforcement of policies.
DATA DISCOVERY + CLASSIFICATION
Where is my sensitive data?
What type of sensitive data?
Dasera continuously classifies sensitive data, then programmatically assigns sensitivity levels, business purpose tags and maps them to known regulations.
Who are my data owners?
Dasera empowers data owners to be effective stewards for their data, resulting in increased ownership and accountability within the organization's data management practices.
Data Security + Automation
What is my security risk posture?
Dasera constantly evaluates data and user behavior to detect overprivileged users, data exfiltration, presence of newly-identified sensitive data, and privacy violations.
Is my sensitive data stored securely?
How do I automate remediation and controls?
Dasera enables automated remediation and controls to effectively manage security risks resulting in improved security, increased efficiency, and reduced human error.
Data Users + Access Governance
Who are the most risky users?
Dasera profiles users to pinpoint problematic data users enabling security and data teams to identify areas to bolster data access controls and mitigate insider threats.
Who should have access to data stores?
Dasera detects access permissions granted to data users and identifies which users have been granted excessive privileges, allowing security teams to adjust permissions based on the principle of least privilege.
Is my data usage in compliance?
Dasera’s user behavior insights will highlight if any of the data users are intentionally or accidentally violating data usage guidelines and immediately notify security teams.
Enter the Data Security Era
Deploy
Flexible deployments including agentless
Integrate
Open platform standard with broad integrations
Automate
Automate and orchestrate manual workflows
Perform
Performs at scale for cloud, hybrid, or on-prem
Enable
Optimizes investigation and remediation workflows
Collaborate
Empowers cross-functional teams and deconstructs silos
Explore Our Featured Resources!
Read the latest on how Dasera is changing the story.